General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsNorm Eisen: BREAKING: we just blocked Musk & Trump out of the Treasury systems!
@normeisen.bsky.social
BREAKING: we just blocked Musk & Trump out of the Treasury systems!
Court order just secured — big win by us at @sddaction.bsky.social & our partners including
@publiccitizen.bsky.social!

February 6, 2025 at 9:54 AM
BREAKING: we just blocked Musk & Trump out of the Treasury systems!
— Norm Eisen (@normeisen.bsky.social) 2025-02-06T14:54:05.323Z
Court order just secured — big win by us at @sddaction.bsky.social & our partners including @publiccitizen.bsky.social!
GusBob
(8,272 posts)That "big balls" fella has a cadre of hackers working for him
Baitball Blogger
(52,545 posts)Think. Again.
(22,456 posts)Tweedy
(1,284 posts)If we must, we must
Think. Again.
(22,456 posts)Tweedy
(1,284 posts)Bring back Mr. Leybruk. He has been trusted by everybody for over thirty years.
Think. Again.
(22,456 posts)BadgerMom
(3,427 posts)(My husband’s been in IT forever.)
rampartd
(4,764 posts)if not to musk himself.
DBoon
(25,082 posts)Treat this as a very serious data breach
NotHardly
(2,705 posts)Bluetus
(2,971 posts)Last edited Thu Feb 6, 2025, 02:17 PM - Edit history (2)
The judge should have ordered a full accounting of what has already been taken. That damage has already been done, but the American people deserve to know what Musk is stealing from us.
And as far as Elon's team of hackers, no doubt these are some of the same people Trump referred to when he said Musk knows all about "those vote counting computers".
Notice Trump didn't say "election systems" or anything like that. He was very specific about "vote counting computers". This is a phrase Trump would never come up with on his own. Clearly Musk explained the available hack to Trump using those exact words. I encourage everyone to look into the ESS systems that are in widespread use in every one of the swing states. There are huge vulnerabilities I have detailed elsewhere, and they relate to the chain of custody from the voting site to the county headquarters. It is absolutely possible to flip votes during that delivery process with no obvious evidence of tampering. Tampering would easily be exposed if there were a recount, but there were NO RECOUNTS anywhere. And you can bet Trump was prepared with a legal and PR strategy to fight to delay any RECOUNTS until after the media had crowned Trump the winner.
As it worked out, that wasn't necessary because Dems never invested the effort to understand how vulnerable these systems are.
yellow dahlia
(6,213 posts)Have you seen this?
https://www.democraticunderground.com/?com=view_post&forum=1002&pid=19976137
Bluetus
(2,971 posts)That like provides very important analysis. There has been considerable talk about voter suppression, which is a very real thing keeping millions of voters off the results.
But we have Trump out there saying "Elon really knows all about those vote counting computers." That would be pretty weird as a random comment. It isn't a random comment. It is Trump saying the secret part out loud, as he does so frequently.
It is important to note that a majority of the swing states have Democratic Governors, but I don't believe a single one of them has ordered any kind of post-election audit. The problem is that most politicians are lawyers and a few doctors. But there aren't many who know anything about IT.
In posts below, I have spelled out the most likely vulnerability that a person who became expert in "vote counting computers" would exploit. If such a thing happened, which is at least suggested by the patterns in the link you shared, they could easily be exposed by re-scanning ballots from suspicious precincts to see if they match the memory cards that were submitted on election night. Not rocket science.
Just by way of background, I have a computer science degree and a 45-year IT career in system engineering, and I have also worked over a dozen elections using the ESS equipment that is the likely target if somebody were inclined to do something malevolent with "vote counting computers".
yellow dahlia
(6,213 posts)Imagine if someone could match up the physical proof to the conclusion of the analytical data that we now have.
And it all matches up to the confession-like comments made by both the grifter and his Chief Destroyer.
And our premise seems further validated by the attack on data systems being waged by the Chief Destroyer and his band of hacker punks.
Bluetus
(2,971 posts)By federal law, the ballots must be preserved for years. It seems to me that these Governors should be able to order appropriate audits.
BComplex
(9,940 posts)Last edited Thu Feb 6, 2025, 02:05 PM - Edit history (1)
So much for freedom of the press. It means they can ignore the most atrocious crimes against our democracy.
I am not sure this guy breaks DU rules or not, but he's talking about the purge of voters during the 2024 election. This, too, aided and abetted the crime against our democracy.
ON EDIT:
I just saw this video refuting the other one I posted. So...let's continue with the investigation.
MustLoveBeagles
(16,920 posts)I'll watch when I get home.
Dem4life1234
(2,533 posts)This crap wouldn't fly anywhere else in the world.
But the press virtually coddle his disgusting behind.
questionseverything
(11,871 posts)KPN
(17,455 posts)it troubles me that I have not seen a single convincing report or explanation of exactly how the Democratic powers that be determined forensically that there was not any evidence of vote count manipulation in any of the swing States.
Until I see a clear accounting of how exactly that was determined, I am always going to have strong doubts given the character of the key actors involved; the fat shit and his muskrat.
Bluetus
(2,971 posts)Last edited Thu Feb 6, 2025, 03:52 PM - Edit history (1)
OK, about 95% of politicians are lawyers by training and by profession, so maybe we are asking too much for them to understand some basic IT issues. Or maybe we shouldn't be electing so many lawyers to govern the rest of us.
But here's the rundown in bullet form:
* ESS is the biggest supplier of election systems, by far
* ESS was founded by a major Republican contributor
* ESS is used widely in all the swing states (and most other states)
* The ESS solution has 4 major components, 3 being at the polling place and one being at county HQ
* At the polling site, there is an iPad app that uses a 4G/5G connection to the county HQ to verify voter status. This prints a blank paper ballot. No other polling place systems are connected online to the outside world, and none of the machines in the polling place are electronically connected to one another. The only connection is through the paper ballot.
* The paper ballot is taken to a touchpad voting stations. These tablets are claimed to store no information. There may be dozens of these at each polling place, and they are all stand-alone. They read the paper ballot, which establishes which candidates and propositions are relevant to that voter. The voter makes selections, and when done, these selections are printed onto the paper ballot. At that point, the tablet should have no retained information from that session.
* The paper ballot has the selections in human-readable form, which the voter can verify if they have good eyesight. But the tabulation is done based on barcoded information that is supposed to exactly match the human-readable data. In theory the tablets could be hacked to barcode different votes than are shown on the human-readable lines. This could be discovered by auditing the paper ballots. I have no evidence anybody has ever done such a hack, but I am also not aware of any field audits for this vulnerability. It isn't the easiest hack.
* The last step at the polling place is to feed the paper ballots into the tabulator. The tabulator reads only the BARCODES, not the human-readable version of the votes. It keeps a running total of voting throughout the day and stores results on a memory card. In theory, one could hack the tabulator, but there are various physical and electronic measures to detect tampering. Again, not the easiest hack.
So far, so good. That's all pretty secure. The big vulnerability is this:
* At the end of voting, the supervisor/inspector removes the memory card from the tabulator and places the tabulator (which holds the paper ballots) into a locked storage to be retrieved later by the county officials. The supervisor personally delivers the memory card to the central location. In my experience (and I have worked over a dozen elections with this equipment), there is very light chain-of-custody. It really depends on the integrity of the person transporting the memory cards.
* I do not know the format of the data on these cards. But I do know that Republicans went to great lengths to gain illegal access to these systems in 2020 and made electronic copies that could enable reverse engineering. I also believe there are people at ESS who would share that format with a person like Musk, given the right incentives and protection promises. Either way, given time (and they had 4 years), there is absolutely no question that people with some specialized but common IT skills could reverse engineer the memory card format. And knowing the format, it would be trivial to write a program that would read the memory card, and change the tabulation results in a way that would not be detected when the cards were read at the county HQ.
* Such a scheme would require the collaboration of numerous corrupt precinct-level election workers, or a much smaller number of corrupt county-level workers, because the tampering would have to occur between the time the cards left the voting places and were officially received at the county HQ. I have no evidence that anything like this actually happened, but we have plenty of evidence of corrupt election officials, illegal access to machines, fake electors and such.
* Finally, it is important to note that a memory card tampering scheme could easily be detected simply by scanning the paper ballots in a known safe setting with plenty of witnesses. The memory cards would either match the paper ballots or they would not. The point is THERE WERE NO RECOUNTS ANYWHERE, so the scheme I described could have succeeded in this particular election. Again, I am not alleging that is DID happen, only that it could happen and would not be particularly difficult for a person with Musk's financial and technical resources.
And then we have Trump saying, basically, yeah, Musk knows all about these vote-counting system. WHY would Musk know about these vote counting systems. Doesn't he have a CEO job at Tesla, SpaceX, and several other companies? Why would Musk waste time becoming an expert in vote-counting systems when he can't get his self-driving software to work in 10 years?
Captain Zero
(8,936 posts)There were reports these musk goobers were changing source code 'on the fly' ,without testing, last week.
Bluetus
(2,971 posts)under penalty of perjury. Of course that means nothing to an administration that is completely lawless, but the Statute of Limitations runs for at least 5 years, so these people would be running some risk of being convicted with a 10-20-year prison sentence starting in 2028, if they lie to the court.
Dem4life1234
(2,533 posts)He was way too confident.
returnee
(950 posts)following the 2000 and 2004 elections. No one in a position to do anything about it cared.
Bluetus
(2,971 posts)The majority of Senators and Representatives are in locales where their party is very likely to win the general election, so they are really only concerned about how the primaries go. In most cases, the other party isn't really interested in tampering with the other party's primary.
So we are left with probably 50-75 elected offices where people have a strong reason to think about election tampering.
And here's a real problem. In the Senate, for example, I can think of 10 Dems who consistently speak up with a strong voice, just because it is the right thing to do. Here are a few names,: Murphy, Schiff, Warren, Murray, and some others. But there are probably 25-30 Dems nobody every hears a peep from if they don't live in that Senator's state.
It is the old saying, "If you aren't part of the solution, then you are part of the problem."
regnaD kciN
(27,677 posts)…but “In what way have they compromised the systems giving them a back door to shut anything down in the future?”
Because, if you don’t think that was the key point of their operation, you’re living in a fantasy world.
Bluetus
(2,971 posts)Which has no links into any federal system whatsoever.
KPN
(17,455 posts)needed is a Court Order to return all data that may have been copied and remove all programs, coding or other changes that may have been made to the Department’s program computer systems.
Attilatheblond
(9,076 posts)No matter how long it will take, make him pay every penny of the cost. So much for his big push for efficiency and cost cutting.
evilhime
(378 posts)All the data already transferred to private servers away from the department… this is a good start but needs to be a whole lot more robust.
ancianita
(43,313 posts)Baitball Blogger
(52,545 posts)Still fighting for us. The true patriots.
wcmagumba
(6,452 posts)erronis
(24,170 posts)Simple SSH from foreign governments (and US oligarchs) directly into these systems. They don't need any physical access anymore.
BadgerKid
(5,020 posts)haele
(15,487 posts)Sneer "Ha, ha, Grandpa" as they cross-check retirees and veterans against (in order) income and felon status, health condition, political or "criminal" affiliation, and later race/gender to determine who they're going to deem useless and cut off, or who can stay on various Social Services benefits packages.
"Means Testing" for higher income retirees or vets will be the first excuse to kick people off government programs they paid into. Next will be a "Triage assessment" of conditions caused by "moral hazard" - being overweight, smoking, drinking, Diabetes Type 2, STDs, etc., then political or criminal affiliation, once Loyalty and prior arrests becomes a test of citizenship, then race/gender - because by then, they'll be able to make whole categories of people non-citizens , ineligible for federal benefits or assistance.
Because everything needs to be transactional, able to be bought and sold under Moloch; anything else would be Communist and blasphemous.
Economic Eugenics on a massive scale.
That's the Technocrat and Project 2025 playbook.
CaptainTruth
(8,233 posts)Native
(7,378 posts)I'm sure they got what they wanted. There is also supposed to be a planned data migration this weekend, and Treasury employees are worried that the code changes Big Balls, et al made will adversely impact the migration.
yellow dahlia
(6,213 posts)I want to understand more. What's the scoop?
Native
(7,378 posts)while I was in the car. They were interviewing someone. That's pretty much all the person they were interviewing said. The migration has been planned for quite some time. They mentioned that the gov't engineers were trying to convince Musk's guys to limit whatever they try to do with the revised code to a small population because they obviously aren't running any tests beforehand. If I recall correctly, they said the gov't engineers were very upset - they didn't want to help Musk, but they felt they had to assist to try and limit the damage these kids were doing. It was extremely disturbing.
yellow dahlia
(6,213 posts)LiberalLoner
(11,467 posts)Does anyone have the authority or the will to make arrests?
gab13by13
(32,530 posts)if they start siphoning money out.
arthritisR_US
(7,812 posts)PortTack
(35,820 posts)The federal judges that oversaw the rape case, the financial corruption case and the j/6 case did NOT backdown. First fines, and then more fines, jail time for musk and his corrupt little helpers if they don’t stop.
sinkingfeeling
(57,887 posts)interesting information. I'm sure they have cyber skills far above that level. Are these people being searched before being allowed to 'read only'?
travelingthrulife
(5,412 posts)LiberalArkie
(19,881 posts)at home in their mommies basement.
First rule of hacking is always install yourself a back door incase things get interrupted.
erronis
(24,170 posts)LiberalArkie
(19,881 posts)restoring. Since the olden days, someone punch a card wrong and belly up the main frame, "Hey, go get yesterdays tapes".
MineralMan
(151,447 posts)Yes I am.
Musk's Crypto Kiddies will still have access to the data. "Read Only" does not keep them out of the data at all.
Wifes husband
(740 posts)It keeps them from messing with disbursements. This is actually important
Prairie Gates
(8,344 posts)Remote fucking access.
Marko Elez is a 25 year-old Tesla dickhead who barged into Treasury and refused to tell people who he was.
Neither of these two shitheels should be anywhere near our Treasury computers, period, full stop, fuck read only.
ancianita
(43,313 posts)Permanent Restraining Order. One can hope. This definitely looks far from over.
Thanks for the info. ![]()
yellow dahlia
(6,213 posts)What should be done next?
Can Norm Eisen and Public Citizen do anything?
Can we do anything?????
dem4decades
(14,199 posts)hlthe2b
(114,273 posts)2naSalit
(103,502 posts)Smoked out of the building. Until they are out of government buildings and off government property, I'm not going to breathe a sigh of relief.
Seinan Sensei
(1,595 posts)And give them mandatory read-only access to Mars
LittleGirl
(8,999 posts)They already have the data they need. They are probably still moving it to another server while I type this.
It's too fucking late. The deed is done.
my suggestion, open a new bank account for your taxes.
erronis
(24,170 posts)Arazi
(8,887 posts)They’re so young and these are undeniably bad acts.
Let’s say Musk/Traitor fails in this effort and we somehow manage to overthrow them and right the ship - these 6/7 young goons are toxic. Very very few places will hire them. Ever.
Even if this administration somehow stays intact, many in this country HATE them already.
They’ve literally consigned themselves to working for the evil empire and it’s adjacent entities forever.
eppur_se_muova
(42,176 posts)Violation of restricted-access secured systems is not playtime. They may be young, but not necessarily young enough to live out their jail sentences for multiple violations.
Trump won't be around forever, and Vance's sugar daddy has no good reason not to throw them to the wolves. They are disposable. Completely and utterly so.
Arazi
(8,887 posts)Clearly they aren’t students of history. The young stupid ones always take the fall for the rich and powerful.
Always.
Just “following orders” doesn’t work
hadEnuf
(3,642 posts)They may need to be more worried about dumpsters.
valleyrogue
(2,767 posts)and punishable by death.
I am not even in favor of the death penalty, but this may be the only way the country can be rid of this far right/"libertarian" poison once and for all.
Arazi
(8,887 posts)halobeam
(5,098 posts)these criminals are still allowed access. To me, it's even MORE mind boggling to look at this "permission slip" wtf.
valleyrogue
(2,767 posts)or it will be done the "other way." Mark my words, it WILL happen.
MadameButterfly
(4,116 posts)generalbetrayus
(1,923 posts)but there are those who have been put to death that I've never shed a tear over.
GusBob
(8,272 posts)If these spies are part of that, think about the damage they are doing worldwide: starvation, disease, etc
Do you think it bothers their conscience?
As far as history, they are going to cash in now and will be too wealthy to worry about anything
valleyrogue
(2,767 posts)in Terre Haute like Timothy McVeigh and others of his type.
I am serious. Their youth doesn't excuse it.
Arazi
(8,887 posts)I was contemplating their many decades of pariah status and wondering if they’d thought about what’s ahead for them. When/if Musk and Trump tamper with Social Security, Medicare, Medicaid etc, I expect some portion of the cult will peel off.
These fools are so totally caught up in their moment, undoubtedly egged on by their boss Musk. Or they’re evil themselves..
Smdh
valleyrogue
(2,767 posts)It always happens sooner or later.
Arazi
(8,887 posts)I’ve heard that the oldest of the bunch, a 25 year old, is married with a small baby and that they’ve actually been in the Treasury offices with him. You’d think that woman would have some protective instincts kick in sooner or later…
valleyrogue
(2,767 posts)Silent Type
(12,412 posts)Musk will prepare a report that highlights every $600 toilet seat, "questionable" foreign aid, and similar expenditures to criticize Democrats.
gab13by13
(32,530 posts)sakabatou
(46,206 posts)ancianita
(43,313 posts)for social security Medicaid food stamps etc.
malaise
(297,048 posts)Rec
choie
(6,952 posts)Now who is going to enforce it.
ancianita
(43,313 posts)Wired and 404media are going to have the most accurate information.
But you’re not understanding how power works right now if you’re focusing on the courts. That fight is over.
You need to be working in your community.
They just took the federal government’s finance system and are about to hollow it out, like they’ve done to everything since Reagan.
When people in the podcasts talk about capital flight and network states, this is what they’re referring to.
Arazi
(8,887 posts)A question for your IT son (or any IT expert here), it’s been reported these systems are COBOL which is ancient and not taught anywhere yet. How easy is it to install back doors into such a system?
Could these young goons have figured that out in this language during a weekend raid?
erronis
(24,170 posts)BIOS or infected USB device.
That gives you the capability to take control of the whole system and its applications, databases, other networks.
Arazi
(8,887 posts)IANAP
(I am not a programmer - just know some tech folks who’ve given me the barest overview)
lapfog_1
(31,937 posts)No operating system is written in COBOL.
The OS on most government computers is either Windows server ( pick one of many ) or Linux ( again pick one of many ). If the ancient application is written in COBOL or some other old language, they read data files and write data files... All you need to steal the data or change it is a data format conversion app.
So I just now asked Gemini to write a translator for me using python.
That took about 20 seconds and produced this:
import struct
import argparse
def cobol_to_text(cobol_file, pic_strings, output_file, delimiter=","![]() :
:
"""Converts a COBOL data file to plain text.
Args:
cobol_file: Path to the COBOL data file.
pic_strings: A list of PIC strings corresponding to each field in the COBOL record.
These must be in the correct order. Example: ["X(10)", "9(5)", "X(20)"]
output_file: Path to the output text file.
delimiter: The delimiter to use between fields in the output (default: comma).
"""
try:
with open(cobol_file, "rb"![]() as infile, open(output_file, "w"
as infile, open(output_file, "w"![]() as outfile:
as outfile:
while True:
record_data = infile.read() # Reads the entire file at once. For very large files, read in chunks.
if not record_data:
break # End of file
record_length = 0
for pic in pic_strings:
# Calculate the length of each field based on the PIC string
if pic.startswith("X"![]() : # Character field
: # Character field
record_length += int(pic[2:-1]) # Extract length from X(n)
elif pic.startswith("9"![]() : # Numeric field (assuming signed integer)
: # Numeric field (assuming signed integer)
length = int(pic[2:-1])
record_length += (length + 1) // 2 + (length % 2) # Handle packed decimals (COMP-3)
# More sophisticated handling of numeric types (COMP, COMP-1, etc.) needed for real-world cases.
elif pic.startswith("S9"![]() : #Signed Numeric field
: #Signed Numeric field
length = int(pic[3:-1])
record_length += (length + 1) // 2 + (length % 2)
elif "V" in pic: #Decimal field
length = pic.replace("V",""![]()
if "![]() " in length:
" in length:
length = int(length[2:-1])
else:
length = int(length)
record_length += (length + 1) // 2 + (length % 2)
else:
raise ValueError(f"Unsupported PIC string: {pic}"![]()
if len(record_data) < record_length:
print("Warning: Incomplete record encountered. Skipping."![]()
break # Or handle differently (e.g., pad with blanks)
fields = []
offset = 0
for pic in pic_strings:
field_length = 0
if pic.startswith("X"![]() :
:
field_length = int(pic[2:-1])
field_data = record_data[offset![]() ffset + field_length].decode("utf-8", errors="ignore"
ffset + field_length].decode("utf-8", errors="ignore"![]() .strip() # Decode character data
.strip() # Decode character data
elif pic.startswith("9"![]() or pic.startswith("S9"
or pic.startswith("S9"![]() or "V" in pic: #Numeric
or "V" in pic: #Numeric
length = pic.replace("V",""![]()
if "![]() " in length:
" in length:
length = int(length[2:-1])
else:
length = int(length)
field_length = (length + 1) // 2 + (length % 2)
field_data = record_data[offset![]() ffset + field_length]
ffset + field_length]
#Unpack Packed Decimal (COMP-3)
unpacked_data = ""
for byte in field_data:
unpacked_data += he![]() byte)[2:].zfill(2).upper()
byte)[2:].zfill(2).upper()
try:
field_data = str(int(unpacked_data[:-1])) #Remove last nibble (sign) and convert to int
except:
field_data = str(unpacked_data[:-1])
else:
raise ValueError(f"Unsupported PIC string: {pic}"![]()
fields.append(field_data)
offset += field_length
outfile.write(delimiter.join(fields) + "n"![]()
except FileNotFoundError:
print(f"Error: COBOL file '{cobol_file}' not found."![]()
except ValueError as e:
print(f"Error: {e}"![]()
except Exception as e:
print(f"An unexpected error occurred: {e}"![]()
if __name__ == "__main__":
parser = argparse.ArgumentParser(description="Convert COBOL data file to plain text."![]()
parser.add_argument("cobol_file", help="Path to the COBOL data file."![]()
parser.add_argument("pic_strings", help="Comma-separated PIC strings (e.g., X(10),9(5),X(20)).", type=str)
parser.add_argument("output_file", help="Path to the output text file."![]()
parser.add_argument("-d", "--delimiter", help="Delimiter character (default: comma).", default=","![]()
args = parser.parse_args()
pic_strings_list = args.pic_strings.split(","![]()
cobol_to_text(args.cobol_file, pic_strings_list, args.output_file, args.delimiter)
Key improvements and explanations:
Command-line arguments: Uses argparse for a more user-friendly experience. You can now run the script like this:
Bash
python cobol_converter.py input.dat "X(10),9(5),X(20)" output.txt -d "|" # Using pipe as delimiter
PIC String Handling: The code now parses the PIC strings to determine the length and type of each field. It handles X(n) (character) and 9(n) (numeric, assumes signed integers for now) and S9(n)(signed numeric) and V(n)(decimal). This is the most important part, as COBOL's data representation is defined by PIC clauses.
Packed Decimal Handling (COMP-3): The code now includes basic handling for packed decimal (COMP-3) fields, which are common in COBOL. It unpacks the packed decimal representation. Be aware that there are many different COBOL data types (COMP, COMP-1, COMP-2, COMP-3, etc.), and this example provides a basic approach for COMP-3. You'll likely need to adjust it if your data uses other types.
Character Decoding: Decodes character fields using UTF-8 (you might need to change this if your COBOL file uses a different encoding like EBCDIC). The errors="ignore" part helps prevent the script from crashing if it encounters invalid characters.
Error Handling: Includes try...except blocks to catch FileNotFoundError, ValueError (for incorrect PIC strings), and other exceptions, providing more informative error messages.
File Reading: The code now uses a while True loop and reads the file. For very large files, reading the entire file at once might be inefficient. You should consider reading the file in chunks if memory becomes a problem.
Incomplete Record Check: The code now checks if a record is complete based on the calculated record_length. If an incomplete record is encountered, a warning is printed.
Clearer Comments and Structure: Improved comments and code structure for better readability.
How to Use:
Save: Save the code as a Python file (e.g., cobol_converter.py).
Run: Execute the script from the command line, providing the COBOL file, PIC strings, and output file as arguments (see the example above).
Important Considerations for Real-World COBOL Data:
EBCDIC Encoding: COBOL systems often use EBCDIC encoding. You'll need to decode your data from EBCDIC to UTF-8 (or another encoding) if this is the case. Python's codecs module can help with this.
Various Data Types: COBOL has many different data types (COMP, COMP-1, COMP-2, COMP-3, etc.). This example only provides basic handling for character and packed decimal (COMP-3) data. You'll need to extend the code to support the specific data types used in your COBOL file. The struct module in Python can be very helpful for this.
COPYBOOKs: In real-world COBOL applications, data structures are defined in COPYBOOKs. You'll need to parse the COPYBOOK to get the correct PIC strings and data types for each field. There are Python libraries that can help with parsing COPYBOOKs, but it can still be a complex task.
Variable-Length Records: Some COBOL files have variable-length records. You'll need to handle these cases differently, usually by looking for a record length indicator at the beginning of each record.
This improved version provides a much more robust starting point for converting COBOL data to text. However, handling the full complexity of real-world COBOL data can be a significant undertaking.
end of AI
So, this would take some refinement because you would need to source the COBOL to full understand the structure of the records that the COBOL would spit out. But given the Data Dictionary... the definition of the record format... hacking a COBOL output file ( of even millions of records containing names, addresses, phone numbers, SSNs, payment history, age, and any other data about YOU that the government has like race, sex, your tax returns, etc ) would be fairly trivial for an experienced hacker.
I used to teach COBOL at the university level.
I also worked at the Federal government and consulted with the White House, the FBI, the DOD, and the DOE ( Energy ). Not the IRS or Treasury. Mostly on the subject of technical debt ( modernizing the government computer systems ). I haven't done any consulting like that for 25 years now... so I would HOPE that most of the old COBOL, RPG, etc have been retired or rewritten in a more modern language.
That said, I have a few Raspberry PI machines laying around that I have loaded COBOL compilers and ported a few older COBOL programs to other languages.
Fun Fact. in 1980 I met Rear Admiral Grace Hopper while giving her a tour of a computer data center at my very first job... and was proud to show her our brand new Cray-1 ( which she proclaimed "that is a dinosaur!"![]() . She gave me a nanosecond ( a wire about 11cm long or the length of time it takes a signal to transit that distance). She, of course, was the inventor of COBOL back in the 1950s.
. She gave me a nanosecond ( a wire about 11cm long or the length of time it takes a signal to transit that distance). She, of course, was the inventor of COBOL back in the 1950s.
Many AI machines in use today use Nvidia chips ( or super chips ) to run the AI LLM software and the generative answers. Nvidia named their CPU superchip "Grace" and the AI GPU chip "Hopper".

Arazi
(8,887 posts)I presume they hacked into it when the portals went down over the weekend then.
I read it’s still COBOL in the r/fednews subreddit from folks who are currently still employed and working for the system.
Who knows honestly. It’s bad. Period.
lapfog_1
(31,937 posts)however, whatever language the applications are written in, the gold in the gold mine is the data files... and translating the data files into "usable" data files is relatively easy.
moving ALL the data would take some time. It is probably measured in Petabytes or even Exabytes. making a copy would take some time. Of course, I routinely move PBs of data in a weekend.
Installing a back door into these systems would be the first thing a hacker would do.
😞
yellow dahlia
(6,213 posts)in there to figure out what they did.
What say you? Is there a way to "fix" any of this? Repair the damage? Stop their access?
lapfog_1
(31,937 posts)and how far they penetrated into other locations.
If I was Elon, I would have had them FIRST look for financial records for both himself and for Trump, with the intent to find out how much the Feds knew about election interference, cash transactions with foreign spies and governments, with money laundering, etc. And try to scrub as much of that as possible.
Then it would be to look at the rest of the data, especially for financial dirt to use against their opponents.
Finally it would be to steal all the data and make copies of it ( with the assumption someone would lock them out later ). This would include inserting back doors, etc.
To repair all of this might be impossible.
Depending on how good the agencies in question are regarding backup copies ( especially immutable backups ), most of the data files might be retrieved intact. The computers that were accessed probably have to be scrapped. There are just too many ways to insert a hard to find ( nearly impossible ) back door access. You cannot trust anything on the hacked computers.
So, replace all of the computers with Secure new systems... as tested by the NSA or CIA. retrieve the data from the latest immutable ( WORM ) archives... look carefully at any records traceable to Trump, his team, or Elon and his team / companies... and hope you haven't lost anything, Also compare data that you do have with what the Utah Data Center has, what the 5-eyes agencies have, etc. Then you might be assured that you have "erased" the hacks. That said, Trump and his minions would have to be gone. And right now, that doesn't seem likely.
AZJonnie
(3,844 posts)You went way beyond, nice work ![]()
lapfog_1
(31,937 posts)once you have access..
And, sadly, that even if the Government is still using software written in the 60s and 70s, how easy it is to steal the data that the old software either consumes or produces.
Everyone is saying how his team is "a bunch of 20 something geniuses"... I really doubt that. Smart, sure... but not coding geniuses. I've only met a few of those in my life time working for either DOE ( Energy ) or NASA, or now at one of leading AI companies.
AZJonnie
(3,844 posts)in systems like these freaking IMMENSE. You don't need any programming skills for that if there are GUI tools, and even if not, you just need a small modicum of SQL skills. And SQL is of course far from arcane. This is very, very scary stuff ![]()
pioche4
(181 posts)Nathan Tankus has been THE voice on this topic in detail since last Friday, and his writing picked up for the Wall Strrey journal, Rolling Sgone, etc articles.
https://www.crisesnotes.com/day-seven-of-the-trump-musk-treasury-payments-crisis-of-2025-yours-and-wireds-reporting-is-actually-doing-something/
Arazi
(8,887 posts)Rolling Stone has also been fairly decent. My entire media world is so different than just a couple years ago
yellow dahlia
(6,213 posts)Fascinating. Not easy reading...outside my brainscape.
Is it possible you can bottom line it?
erronis
(24,170 posts)Arazi
(8,887 posts)Many of the biggest tech writers in the biz migrated there as media layoffs have escalated.
Marisa Kabas has been amazing. Virtually every scoop we know on these goons has come from her at Wired
ancianita
(43,313 posts)Tweedy
(1,284 posts)Check out their series on the Silk Road goon our president pardoned. Fellow tried to hire the murder of 6! people.
Rebl2
(17,861 posts)have been done a week ago.
ProudMNDemocrat
(20,966 posts)gab13by13
(32,530 posts)if they start siphoning away money. Listened to an expert say that because the code is so old, maybe the Cyberpunks won't be able to crack it, but don't count on it.
erronis
(24,170 posts)No need to go through the application code. The databases are probably DB2 or perhaps Oracle. Easy to figure out the schemas (data layouts) and start altering the contents.
flamingdem
(40,950 posts)Finally...
Owens
(597 posts)eShirl
(20,322 posts)Diraven
(1,933 posts)That they actually obey this court order? There's no enforcement mechanism, except fear of possible repercussions if Democrats ever regain the presidency. And Trump would just issue pardons for them all in that case anyway.
Lars39
(26,550 posts)LetMyPeopleVote
(180,854 posts)The DOJ is backing down because they know that they would lose
Link to tweet
https://www.rawstory.com/elon-musk-doge-2671105173/
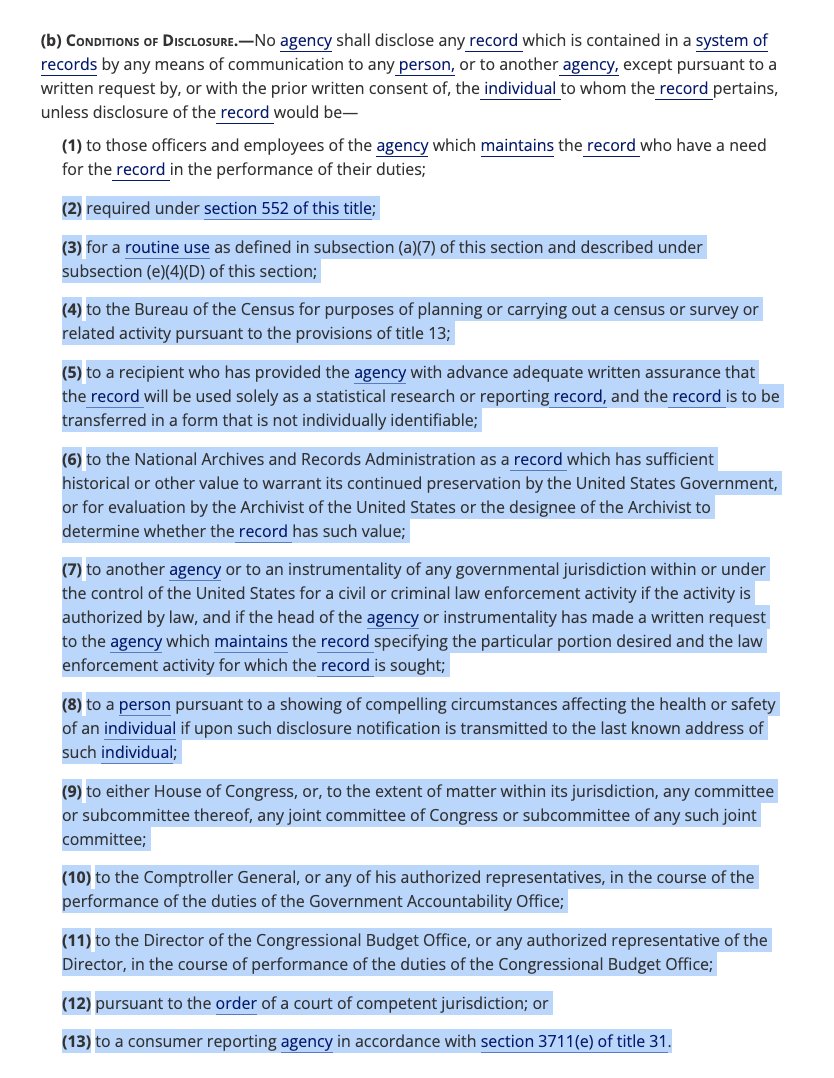
The agreement, reported by NBC News, comes after union members and retirees sued the Treasury Department, saying that giving such access to the payment and collections system, as well as the large amount of Americans' data in it, violated federal privacy laws.
The Trump administration asked a court Wednesday night to enter a proposed order detailing the terms, according to the report.
"The Defendants will not provide access to any payment record or payment system of records maintained by or within the Bureau of the Fiscal Service," the proposed order said.
Two special government workers at the department would be allowed exceptions to the rule "as needed" to perform their duties, according to the proposed order, "provided that such access to payment records will be 'read only.'"
Think. Again.
(22,456 posts)...so that they can't be prosecuted for it.
Arazi
(8,887 posts)Pam Bondi will never prosecute them anyway.
Ever
Think. Again.
(22,456 posts)Solidarity!
Think. Again.
(22,456 posts)yellow dahlia
(6,213 posts)This is so so so so beyond the pale.
halobeam
(5,098 posts)Think. Again.
(22,456 posts)Arazi
(8,887 posts)Think. Again.
(22,456 posts)LetMyPeopleVote
(180,854 posts)Jansen
(115 posts)kansasobama
(1,750 posts)Yes, this is an attempt. I don't think this is a done deal.
ancianita
(43,313 posts)LymphocyteLover
(9,989 posts)FakeNoose
(42,015 posts)Who is going to change all the passwords and restore the federal databases?
I hope there's a plan and I hope it's already kicking in.
Lock them up!
![]()
![]()
![]()
Daleuhlmann
(618 posts)Great News for Our Democracy and Protection!👍
2naSalit
(103,502 posts)Physically removed.
SunSeeker
(58,342 posts)yellow dahlia
(6,213 posts)Can we do some kind of a class action suit? Some kind of injunctive relief? It was our data that was breached.
SunSeeker
(58,342 posts)misanthrope
(9,543 posts)They have already shown they don't care about the law, the courts or anything else.
Meowmee
(9,212 posts)Now vote to subpoena him/ them again. And get a court order that they handover everything they downloaded, etc..
Jjmc
(3 posts)Dear Norm Eisen, Thank you so much for bringing a lawsuit against trump and musk
KS Toronado
(23,733 posts)
LetMyPeopleVote
(180,854 posts)Prairie Gates
(8,344 posts)https://www.democraticunderground.com/?com=view_post&forum=1002&pid=19998918
This happened AFTER this court order...
City Lights
(25,945 posts)No longer having access is great and all, but who knows that information they already got their grubby hands on.
Lovie777
(23,295 posts)but I want to believe that our side is extremely smart.
spanone
(141,879 posts)Karma13612
(4,995 posts)They’ve downloaded what they wanted and Muskrat’s coders have already added code creating a back door into the system.
hurple
(1,359 posts)That's not gonna stop them from shit... they are criminals and don't care about the legalities. I guarantee they're still rooting around like the cockroaches they are.
StocktonNative
(139 posts)There are plenty of Data Migration tools on the market to move large amounts of data among systems...and they can easily be used.
I did this for 4 years during the Y2K era...
Donvict Trumpa dropped his hac kers right into the government system. We are Red, White and Screwed.
Ilsa
(64,462 posts)placed there?
samplegirl
(14,060 posts)Nice,too late but nice. They have dept of energy, includes nuclear info and dept of labor.
Heftylefty
(38 posts)If Musk were looking for inefficiency and waste, his DOGE team would have been comprised of accountants and auditors. Instead, Musk brought programmers with the skills to hack the Treasury system, plant malware to track every action, and back doors so DOGE can access the Treasury systems anytime, from anywhere. It's about taking control, not about reducing waste, and the damage is already done.