2016 Postmortem
Related: About this forumRandySF
(86,250 posts)THAT doesn't look good.
Depaysement
(1,835 posts)Leave easily traceable evidence of your actions, creating user names tagged "Bernie." Not exactly surreptitious activity. What's up with that?
Something is rotten and it ain't in Denmark.
JaneyVee
(19,877 posts)And this is company data, they may not even have known actions were being logged.
Depaysement
(1,835 posts)JaneyVee
(19,877 posts)Depaysement
(1,835 posts)And you have no evidence to support your claim that they accessed from their own domain and those were their domain user names.
Jarqui
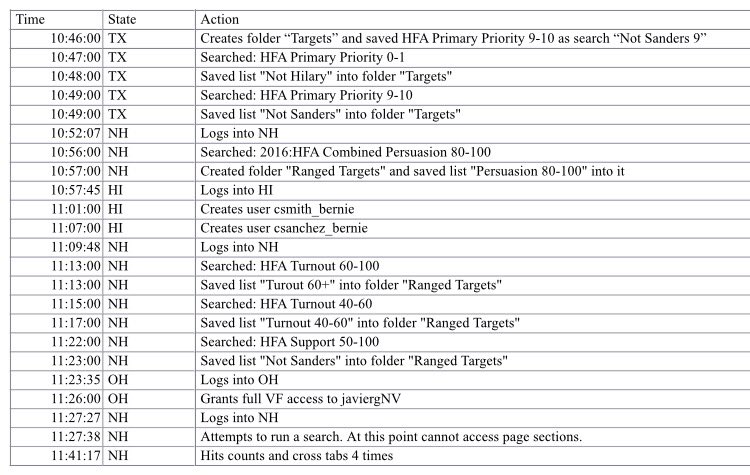
(10,925 posts)1. He's looking at "Not Hillary" list
2. He's looking at priority 0-1 and then priority 9-10 in TX - he's missing a bunch in between - you'd get it all if you were trying to steal the data or you'd be interested in only the higher or lower priorities
3. Again, he goes into NH and just gets Persuasion 80-100 range - why not the other ranges if you were stealing data?
4. He logs into HI and creates two new "_Bernie" logins not "_Hillary" or "_OMalley" - hardly trying to keep eyes away from the Sanders campaign
5. He goes back into NH and gets a couple of ranges of Turnouts and one range Support - again, incomplete sets and middle of the road - not convincing that this is the best data for them to get
6. Logs into OH and gets full VF access .. and does nothing with it
7. Much of the time, he's generating lists - which are usually just item identifiers - not the whole data.
This is not a guy downloading gobs of data or getting a contiguous chunk of user data. I don't know the application but he looks like he's doing as he said - bouncing around seeing what was open/available to him by sampling ranges of various fields and generating lists - not full data dumps or reports.
PowerToThePeople
(9,610 posts)Good post.
![]()
JaneyVee
(19,877 posts)Forgot that part?
winter is coming
(11,785 posts)My point but in much more and better detail. Well done. ![]()
joshcryer
(62,536 posts)And it's not clear that the "_bernie" designation is manually created, it could be the system assigning their username "csanchez" to group "_bernie."
Jarqui
(10,925 posts)- add logins - maybe that's supposed to be handled by the vendor to some extent.
Separate lists for 20% of the data? Leaving a big hole in 80% of the data? That has really limited usage -particularly in that much of it was middle of the road - not top or bottom ranges.
And much of that data doesn't even seem to distinguish who it belongs to - it probably includes Hillary but they have no separation between the campaigns.
If these things like "Primary Priority""Turnout""Support" are fields the Clinton campaign created and entered, you'd probably need to understand the rules of how they derived the range for them to have much meaning. where is that?
They have the above logs or logs like them for the above and other users. They have a darn good idea what the Sanders campaign did. This talk about an audit and wanting a declaratino from Sanders when they already have this smells like a colossal pile of BS.
I hope the judge kicks the crap out of DWS and the DNC. This is a big hunk of nonsense that should never have been made public. Clearly, it was done for the sole purpose of trying to hurt the Sanders campaign - not because anything sinister like stealing or a significant data loss had occurred.
This is a 2008 deja vu and yes, it's on her because even though a candidate should not, Hillary obviously effectively controls the DNC or they're very much biased and on her side in this contest. The DNC should not be so biased or in the camp of one of the candidates. It's a disgrace.
Hell Hath No Fury
(16,327 posts)looks like it supports the Sander's IT guy's story. ![]()
Who the heck creates a "user" with BERNIE'S OWN NAME in it if they're trying to do skulduggery??? Seriously, that just doesn't make sense. ![]()
Hate to break it to you but my mind has been put at ease with that screenshot.
JaneyVee
(19,877 posts)They were able to breach from their side. And they may have not been aware their actions were logged. This is from company.
Hell Hath No Fury
(16,327 posts)just assumes his actions aren't being logged? Seriously?
JaneyVee
(19,877 posts)roguevalley
(40,656 posts)who 'leaves' a firewall down after being told about it two months ago? Him?
Go Vols
(5,902 posts)OilemFirchen
(7,288 posts)So he knows he's being logged, searches and downloads proprietary data.
Seriously?
Luminous Animal
(27,310 posts)Hell, I'm an end user and I know that.
joshcryer
(62,536 posts)seabeyond
(110,159 posts)joshcryer
(62,536 posts)Tells you the intelligence of these dipshits.
Fire them all.
Stop fucking making excuses.
workinclasszero
(28,270 posts)Right here.
MeNMyVolt
(1,095 posts)PowerToThePeople
(9,610 posts)My dns server blackholes many known malicious web domains, it is very likely this photo is hosted somewhere that people may not wish to expose their computer systems to.
edit - I was able to get to the image (possibly a browser flaw). Looks like an excel spreadsheet that someone created. I can make something just like that in a matter of minutes with whatever information, true or false, I wish to put into it.
![]()

Kick in to the DU tip jar?
This week we're running a special pop-up mini fund drive. From Monday through Friday we're going ad-free for all registered members, and we're asking you to kick in to the DU tip jar to support the site and keep us financially healthy.
As a bonus, making a contribution will allow you to leave kudos for another DU member, and at the end of the week we'll recognize the DUers who you think make this community great.