2016 Postmortem
Related: About this forumAudit #1 Shows 9x Bernie staffers saved stolen data into their own account.
And this is just audit #1:
http://www.scribd.com/mobile/doc/293643104/Sanders-Campaign-Audit-Sheet-1
DURHAM D
(33,091 posts)leftofcool
(19,460 posts)It was all DWS's fault and all Hillary's fault.
seabeyond
(110,159 posts)NCTraveler
(30,481 posts)The stupidity of the guy the fired talking to the press yesterday. He flat out admitted they knew it was wrong and kept going. We now know it's even more nefarious.
JaneyVee
(19,877 posts)Until any stolen data is isolated and destroyed.
NCTraveler
(30,481 posts)Armstead
(47,803 posts)sufrommich
(22,871 posts)NCTraveler
(30,481 posts)Thanks.
Armstead
(47,803 posts)I know , you're not referring to him personally....But my self-acknowledged deliberate hyperbole comes close
JaneyVee
(19,877 posts)Good one, I must admit
NCTraveler
(30,481 posts)It's a bigger deal than you think.
seabeyond
(110,159 posts)He is responsible, ultimately for what others did. How he has handled it to this point is a view of how he will be president. Ignore the wrong, shift the blame, then throw a tantrum because people are focusing on the theft and not the "important" stuff.
Kentonio
(4,377 posts)JaneyVee
(19,877 posts)That should be good enough. A bigger question is why don't you care?
NCTraveler
(30,481 posts)What a strange response. Seems pretty clear that all that's left.
Kentonio
(4,377 posts)NCTraveler
(30,481 posts)My response works for them as well when it comes to your out of place comment.
Kentonio
(4,377 posts)It had absolutely nothing to do with you, and I can only assume you just misread it as a reply to you. Not a big deal, easy enough for anyone to do sometimes.
I'm more confused by why you appear to be doubling down on that error instead of just admitting it.
cwydro
(51,308 posts)"Well, I wasn't trying to be sneaky."
In other words - I stole that stuff right in the open, so there. ![]()
RKP5637
(67,112 posts)Jarqui
(10,925 posts)had access to other campaigns data into a newly created folder to gather the evidence of the security problem
they did so knowing the linked audit of their activities was available
They did not save or "steal" the other campaigns actual voter data
JaneyVee
(19,877 posts)If you can't understand that then this might be over your head. THEY STOLE DATA.
Jarqui
(10,925 posts)Or generate a detailed report where they could recover the data?
There is none. To steal data you have to have something that shows the actual data got stolen.
What they have are lists of item identifiers (probably of voters - internal ID numbers). And those lists were generated by Clinton or O'Malley fields. But most of what I've seen is partial selections so they cannot construct complete data for those fields - even within a state.
To prove/collect evidence of a security breach, they couldn't do so with their own data because their security would already give them full access to their own data. They HAD to prove it by using data fields that were not theirs. And that's what they did by generating those lists.
If they were stealing data, they'd generate a big detailed report with several other campaigns fields for an entire state or they'd download the voter file with the other campaigns data. They did not do that.
So no, they did not steal data. They gathered evidence of a security breach by generating lists of voter IDs that they all have access to (because they share things like addresses and phone numbers) . Their activity logs are pretty clear. Their activity logs show no evidence of bulk data theft.
If you don't accept that, then using those activity logs, prove me wrong. That's a rhetorical challenge because from those logs, I already know how its going to turn out.
JaneyVee
(19,877 posts)ejbr
(5,892 posts)Jarqui
(10,925 posts)I'm sure the Clinton campaign tracks many fields. Having partial lists of samples of those in various states doesn't allow one to get a full array of the data. And you'd need the key for what the data in those fields means (though some of it could be projected).
And we didn't see a progressive effort to get every field for every voter file with those lists so that they could reconstruct the data.
This apparently is Josh's - he's the guy they allege created new IDs
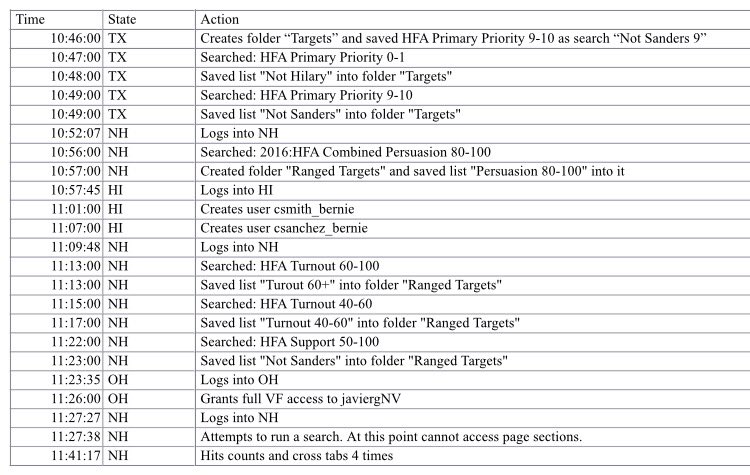
He's all over the map. He's not systemically working on one field in one state. He's bouncing around from state to state grabbing lists for various fields that do not provide the data for all of the field in one state.
If you were stealing HFA Primary data for example, you'd expect to see (I'm projecting some here)
HFA Primary 0-1
HFA Primary 2-3
HFA Primary 4-5-6
HFA Primary 7-8
HFA Primary 9-10
to fill in all the blanks in the voter data that the other campaigns had in those fields. But he only generated two lists HFA Primary 0-1 and HFA Primary 9-10 - some were "not Hillary", some "not Sanders" so it was a mixed bag.
It was an incomplete set in Texas. Instead of finishing "stealing" all of the data for those fields in Texas, he moves on. He then gets Hew Hampshire Persuasion 80-100 - obviously not all the Persuasion data and then he moves on again to create a couple of users in "HI". Then back to NH where he gets a couple of selections on turnout - but not all of them. Then one selection on Support but not all of them.
That is not the activity pattern of someone trying to steal data because he's getting a bunch of incomplete chunks of select lists so they cannot recover a full set of data for that field in the state he was in.
And that's the activity of the data director - a guy who would know what to do if he wanted to steal data.
I'm sorry but the disconnect appears to be with you. The above is not the activity one would see of a person stealing data. It reflects the behavior of what Josh said he was doing - proving a data security breach applied to various fields in various states.
joshcryer
(62,536 posts)They're excluding people turnout in the 60-100 range for Hillary for America. This way they don't waste their time on those lists.
JaneyVee
(19,877 posts)SidDithers
(44,333 posts)I wonder if that's Javier Gonzalez, the Sanders Nevada field director.
http://www.buzzfeed.com/adriancarrasquillo/bernie-sanders-hires-high-profile-dreamer-activist-for-latin#.hdGO2ZDrrZ
If so, it looks to me like staffers were trying to direct data, or access, to those in the field who could use it to help the campaign.
Sid
bkkyosemite
(5,792 posts)Sancho
(9,211 posts)why are they resisting an investigation? Why fire the staff?
No one needed to "prove" something by downloading strategic information. That's silly.
No one believes it. They need to fess up and the only thing they need to "prove" is that the downloads are deleted - unless it's already spread out all over 10 states!!!
If they don't submit to a serious investigation, then we know they are "crooks".
Jarqui
(10,925 posts)I feel like he was a sacrificial lamb. His activity log supports what he claimed he was doing - gathering evidence of a security breach that had happened to them before. He was protecting the organization he was working for.
You often do need proof because when the vendor closes the open security door, you're otherwise stuck - without any evidence it ever happened. The vendor can just deny it ever happened - end of story. And this had happened to the Sanders campaign more than once before and the Sanders campaign feel confident another campaign got their data. So don't ignore the context in which this happened. You get ripped off a couple of times while the definition of insanity is to keep doing the same thing over and over again and expecting different results.
From those logs, I don't think the Sanders campaign would have any problem submitting to an investigation. Where they'll have trouble getting someone to go along with an investigation is last October, when the Sanders campaign feels another campaign took their data. And that's quite a curious thing here. Why the big fuss now and not the big fuss when the Sanders campaign was victimized?
Democratic Nepotism for Clinton ?
joshcryer
(62,536 posts)And they fired him because despite what was said, he just came off as guilty. They worked with him, they knew each other on a personal level, they take him to a room, and he basically exudes guilt. Because he and the people working with him were guilty.
The specificity of the lists is too coincidental to just be data checks. You don't grab useful ranges. Ranges like 1-2, then 11-12, then 21-22 or something, just to prove a range could be grabbed and it went up and down the dataset. Better yet, run a random number generator and pick 5 random ranges and document it with a cell phone video. Document the whole thing even.
I thought initially it was snooping and checking but I'm sorry, the way the data was grabbed, it's inarguable that it was willful data gathering.
Sancho
(9,211 posts)they were obviously looking at targeted data for campaign strategy.
There's no way to defend it so it's silly to try. No one believes it, and the logs prove what they were looking for was specific.
The previous problem was on a different system (same vendor), and records showed that no one got Bernie's data from that time. If anyone got Bernie's information, it was not from this vendor.
Hillary has much more to lose than Bernie in this - her organization is many times larger and more sophisticated.
Why not turn over the computers on Wednesday? The only reason I can think of is that there was evidence of something on them that the Sanders campaign didn't want to be seen - and they needed time to clean it up. Maybe much more than this data breech.
Jarqui
(10,925 posts)They absolutely were evidence of a leak and that is utterly beyond any rational dispute
All parties agree the Sanders folks were accessing data that belonged to another campaign. No one has argued any differently.
All parties agree that their ability to do so came about through a problem with what the vendor did - which compromised the security = A leak!!
In order for the Sanders people to be able to do what they did with other campaigns data, there had to be some sort of leak. Right. Pretty basic logic.
They were not "obviously looking at targeted data for campaign strategy." because they were all over the map - getting incomplete data in various states with various fields.
If the "priority" data was so vital, why wouldn't they get "priority" data in every state? Why just Texas? And why focus on Texas first - isn't Iowa and NH more important? And why miss a bunch of the priority data in Texas "Priority 2-8"? It doesn't make sense. You'd want a more complete or contiguous data array for that field - rather than just high and low priority. But that's not what he went for. He then darted off to another state. And so on through taking bits or excluding bits of other fields in other states.
If you really wanted to steal that data, you'd just go around the application that looks like the only place they had security on it and go under the hood and steal it. They'd have no application log to prove anything at the file level. The system design for security on that system smells pretty bad when an application bug leaves the emperor with no clothes. There's something wrong deeper than that application bug. There should be more than one line of defense.
By the sounds of it, a half ass programmer could get that data and nobody would be the wiser.
Sancho
(9,211 posts)The only logical reason is to have time to clean up the mess and cover their tracks.
If they weren't doing anything, then the techs could come over and be done in a jiffy!!
The Sanders campaign was FORCED to come to an investigation by cutting them off. Even now, so evidence is probably gone and some staff will be hard to find.
No need to argue about programming. The behavior reeks of guilt and cover up.
joshcryer
(62,536 posts)They got lists for people who were over 70% going to vote for Clinton (people to exclude) and 30% for Clinton (people to target).
Then they escalated former NGP VAN architect Ali Nikseresht so he could have a look.
I'm sure that was all on the up and up and just your regular run of the mill "hey I gained access."
When I was a white hat I tended to close the exploit and leave a text file in the root directory. ![]()
sufrommich
(22,871 posts)now moved onto explaining that what they saved wasn't important.Next up: overzealous staffer.
moobu2
(4,822 posts)see? It's the blackout corporate media conspiracy and Bernie Sanders staffers were just trying to prove it by stealing Hillarys voter info and it's DWS fault..see?
MohRokTah
(15,429 posts)Sancho
(9,211 posts)Regardless, I wonder if the Sanders people don' want an investigation (like turning over computers) because they know of other nefarious things they've been doing that will show up besides this one data breech?
Do they want to avoid putting staff under oath?
Hmmmm.....
NurseJackie
(42,862 posts)Sancho
(9,211 posts)I was watching MSNBC this am. I typed some of their comments. Sorry if I got them off a little, but I'm sure someone can check accuracy later. All from the panel:
"Bernie is under fire for the first time."
"Staffer was fired."
"Hillary is surging".
"Launching an independent audit. Further action will be taken."
"tempest in a thumb drive".
"bad explanation",
"Sanders is running an outsider campaign and now cheating.",
"like a student trying to justify plagiarism", "not just one person",
"Sanders opened the door and looked at the panties".
"if Hillary had done this, it would be a Congressional investigation",
leftofcool
(19,460 posts)That was David Corn.
workinclasszero
(28,270 posts)Judge they left the door open so naturally we had to go in and steal everything that wasn't nailed down!! ![]()
![]()
![]()
JaneyVee
(19,877 posts)Starry Messenger
(32,382 posts)Gman
(24,780 posts)After 6 staffers ran 24 queries and saved data from the Hillary campaign is they were only trying to document the error.
Number 1, first and foremost, they knew full well they were not allowed to access Hillary's data under ANY circumstances. Doing so showed not only a lack of ethics and total dishonesty, but quite possibly was illegal.
A judge would laugh in their faces for saying, "We were only trying to document it."
they had the chance to pull a bunch of Hillary data and they did it. All the crying, whining and total fake outrage to distract and redirect only makes it worse.
In my business, certain events trigger a protocol, and even the youngest and lowest level employees know to STOP, step away from the controls, REPORT to the proper outside authority and then DOCUMENT the crap out of what happened.
They may not speak to anyone other than reporting the incident to top managers AFTER they reported the incident to authorities (that way they know we did not collude to make our stories match up first). We only speak to our attorney and to the authorities until everything is cleared up.
It is a cover-your-ass protocol so it doesn't look like the organization attempted to manipulate or cover up if it does end up being a legal matter. And we are not campaigning to be leader of the free world, either. We are very small potatoes, comparatively. And yet my people would have handled this issue better.
Gman
(24,780 posts)And know it well.
I've seen it happen before. Perfectly bright and very intelligent people who know full well the protocol and know full well there is a record of everything, do something stupid and and claim they just don't understand that they did anything wrong.
Their own unethical tendencies is what got them busted. And they have no one else to blame.
JaneyVee
(19,877 posts)PowerToThePeople
(9,610 posts)Nothing but a smear attempt.
See you in court.
JaneyVee
(19,877 posts)Fearless
(18,458 posts)Cali_Democrat
(30,439 posts)LOL...what?
Hoyt
(54,770 posts)Alfresco
(1,698 posts)
Kick in to the DU tip jar?
This week we're running a special pop-up mini fund drive. From Monday through Friday we're going ad-free for all registered members, and we're asking you to kick in to the DU tip jar to support the site and keep us financially healthy.
As a bonus, making a contribution will allow you to leave kudos for another DU member, and at the end of the week we'll recognize the DUers who you think make this community great.