Welcome to DU!
The truly grassroots left-of-center political community where regular people, not algorithms, drive the discussions and set the standards.
Join the community:
Create a free account
Support DU (and get rid of ads!):
Become a Star Member
Latest Breaking News
General Discussion
The DU Lounge
All Forums
Issue Forums
Culture Forums
Alliance Forums
Region Forums
Support Forums
Help & Search
friendly_iconoclast
friendly_iconoclast's Journal
friendly_iconoclast's Journal
October 29, 2013
And it looks like some of the guys in Antibalas (the premier Afrobeat band around)
are a little melanin-challenged:
http://en.wikipedia.org/wiki/Antibalas

"..his choice of music genre". You need to educate yourself on the history of Afrobeat:
Seems like the guy who pretty much invented it didn't have a problem
with white guys playing it...
And it looks like some of the guys in Antibalas (the premier Afrobeat band around)
are a little melanin-challenged:
http://en.wikipedia.org/wiki/Antibalas

October 10, 2013
Also discussed here:
http://www.theguardian.com/world/2013/oct/04/tor-attacks-nsa-users-online-anonymity
http://sync.democraticunderground.com/1014611160
How The NSA Deploys Malware: An In-Depth Look at the New Revelations
https://www.eff.org/deeplinks/2013/10/how-nsa-deploys-malware-new-revelationsHow The NSA Deploys Malware: An In-Depth Look at the New Revelations
October 8, 2013 | By Dan Auerbach
We've long suspected that the NSA, the world's premiere spy agency, was pretty good at breaking into computers. But now, thanks to an article by security expert Bruce Schneier—who is working with the Guardian to go through the Snowden documents—we have a much more detailed view of how the NSA uses exploits in order to infect the computers of targeted users. The template for attacking people with malware used by the NSA is in widespread use by criminals and fraudsters, as well as foreign intelligence agencies, so it's important to understand and defend against this threat to avoid being a victim to the plethora of attackers out there.
Deploying malware over the web generally involves two steps. First, as an attacker, you have to get your victim to visit a website under your control. Second, you have to get software—known as malware—installed on the victim's computer in order to gain control of that machine. This formula isn't universal, but is often how web-based malware attacks proceed.
In order to accomplish the first step of getting a user to visit a site under your control, an attacker might email the victim text that contains a link to the website in question, in a so-called phishing attack. The NSA reportedly uses phishing attacks sometimes, but we've learned that this step usually proceeds via a so-called “man-in-the-middle” attack.1 The NSA controls a set of servers codenamed “Quantum” that sit on the Internet backbone, and these servers are used to redirect targets away from their intended destinations to still other NSA-controlled servers that are responsible for the injection of malware. So, for example, if a targeted user visits “yahoo.com”, the target's browser will display the ordinary Yahoo! landing page but will actually be communicating with a server controlled by the NSA. This malicious version of Yahoo!'s website will tell the victim's browser to make a request in a background to another server controlled by the NSA which is used to deploy malware...
...The NSA has a set of servers on the public Internet with the code name “FoxAcid” used to deploy malware. Once their Quantum servers redirect targets to a specially crafted URL hosted on a FoxAcid server, software on that FoxAcid server selects from a toolkit of exploits in order to gain access to the user's computer. Presumably this toolkit has both known public exploits that rely on a user's software being out of date, as well as zero-day exploits which are generally saved for high value targets.2 The agency then reportedly uses this initial malware to install longer lasting malware.
October 8, 2013 | By Dan Auerbach
We've long suspected that the NSA, the world's premiere spy agency, was pretty good at breaking into computers. But now, thanks to an article by security expert Bruce Schneier—who is working with the Guardian to go through the Snowden documents—we have a much more detailed view of how the NSA uses exploits in order to infect the computers of targeted users. The template for attacking people with malware used by the NSA is in widespread use by criminals and fraudsters, as well as foreign intelligence agencies, so it's important to understand and defend against this threat to avoid being a victim to the plethora of attackers out there.
Deploying malware over the web generally involves two steps. First, as an attacker, you have to get your victim to visit a website under your control. Second, you have to get software—known as malware—installed on the victim's computer in order to gain control of that machine. This formula isn't universal, but is often how web-based malware attacks proceed.
In order to accomplish the first step of getting a user to visit a site under your control, an attacker might email the victim text that contains a link to the website in question, in a so-called phishing attack. The NSA reportedly uses phishing attacks sometimes, but we've learned that this step usually proceeds via a so-called “man-in-the-middle” attack.1 The NSA controls a set of servers codenamed “Quantum” that sit on the Internet backbone, and these servers are used to redirect targets away from their intended destinations to still other NSA-controlled servers that are responsible for the injection of malware. So, for example, if a targeted user visits “yahoo.com”, the target's browser will display the ordinary Yahoo! landing page but will actually be communicating with a server controlled by the NSA. This malicious version of Yahoo!'s website will tell the victim's browser to make a request in a background to another server controlled by the NSA which is used to deploy malware...
...The NSA has a set of servers on the public Internet with the code name “FoxAcid” used to deploy malware. Once their Quantum servers redirect targets to a specially crafted URL hosted on a FoxAcid server, software on that FoxAcid server selects from a toolkit of exploits in order to gain access to the user's computer. Presumably this toolkit has both known public exploits that rely on a user's software being out of date, as well as zero-day exploits which are generally saved for high value targets.2 The agency then reportedly uses this initial malware to install longer lasting malware.
Also discussed here:
http://www.theguardian.com/world/2013/oct/04/tor-attacks-nsa-users-online-anonymity
http://sync.democraticunderground.com/1014611160
October 3, 2013
Is there any way for DU to determine if multiple IP addresses are using a single name?
I suspect certain member names are being used by multiple posters, and am wondering
if the admins are OK with this.
October 3, 2013
For those unfamiliar, they would look like this:
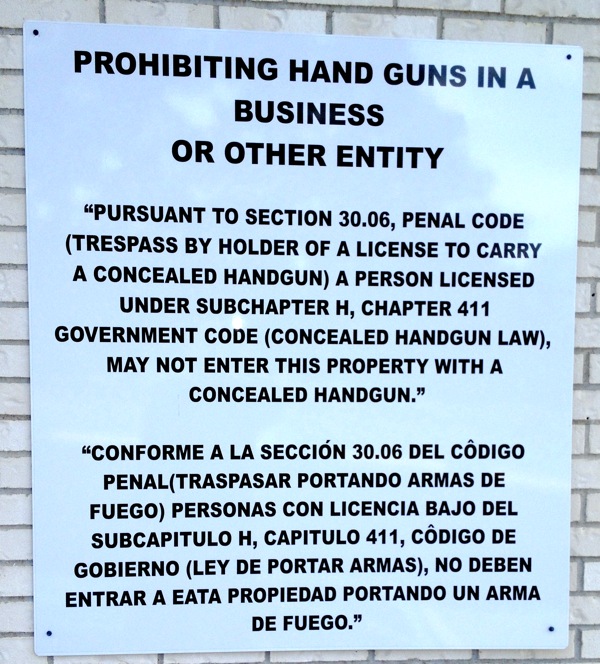
In Texas, anything else is not a legal prohibition on the carriage of concealed weapons.
Unless a SB in Texas has one of these by the front door, concealed handguns are still allowed there.
Without one of those in every Lone Star Starbucks, you can be certain that Howard Schultz
merely offered up some fine words that have gulled the credulous
into thinking they've achieved something...
Here's how we can tell if Starbucks is sincere about what they say re guns:
Do Texas Starbucks have '30.06 signs' posted prohibiting guns?For those unfamiliar, they would look like this:
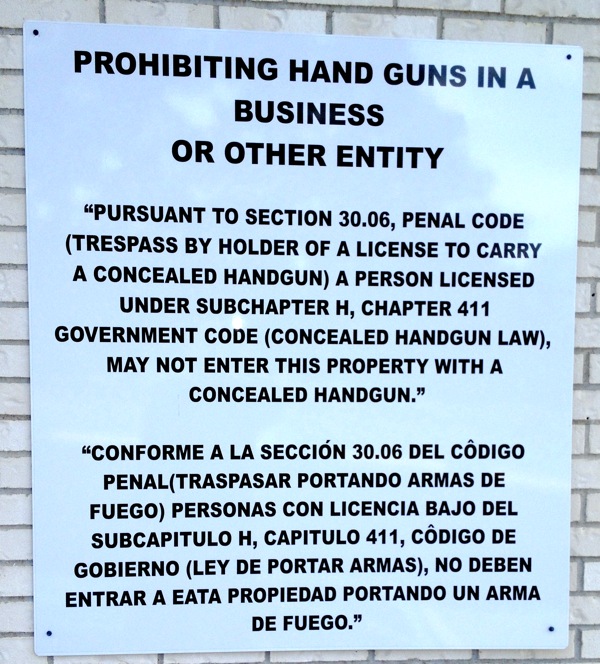
In Texas, anything else is not a legal prohibition on the carriage of concealed weapons.
Unless a SB in Texas has one of these by the front door, concealed handguns are still allowed there.
Without one of those in every Lone Star Starbucks, you can be certain that Howard Schultz
merely offered up some fine words that have gulled the credulous
into thinking they've achieved something...
Profile Information
Member since: Fri Sep 8, 2006, 12:47 PMNumber of posts: 15,333